Windows Sandbox: Safeguarding Your System from Malicious Software and Threats
I'm Matthew, a cybersecurity enthusiast, programmer, and networking specialist. With a lifelong passion for technology, I have dedicated my career to the world of cybersecurity, constantly expanding my knowledge and honing my skills. From a young age, I found myself captivated by the intricate workings of computers and networks. This fascination led me to pursue in-depth studies in the fields of networking and cybersecurity, where I delved deep into the fundamental principles and best practices. Join me on this exciting journey as we explore the multifaceted world of technology together. Whether you're a beginner or a seasoned professional, I am here to share my knowledge, discuss the latest trends, and engage in insightful discussions. Together, let's embrace the ever-changing world of tech and navigate the complexities of cybersecurity with confidence and expertise.
As a cybersecurity specialist, ensuring maximum safety when handling sketchy computer-related tasks is super important. It has never been easier thanks to Windows Sandbox’s distinct ability to provide a secure isolation environment within your device's operating system. Designed specifically for running uncertified files and applications without undermining your computer's integrity, it acts as an impenetrable shield from malignant software or any damaging procedures executed unknowingly by inappropriate programs installed on your machine. In this article, we will explore the remarkable features of Windows Sandbox, a powerful tool provided by Microsoft to protect your system from potential security risks. We'll delve into its key characteristics and provide practical steps for configuring it to ensure optimal performance.
Getting Started with Windows Sandbox
Before diving into the configuration options and advanced features, let's quickly cover the basics of setting up and running Windows Sandbox on your Windows 10/11 Pro machine. Follow these simple steps:
Open the Start menu and search for "Windows Features."
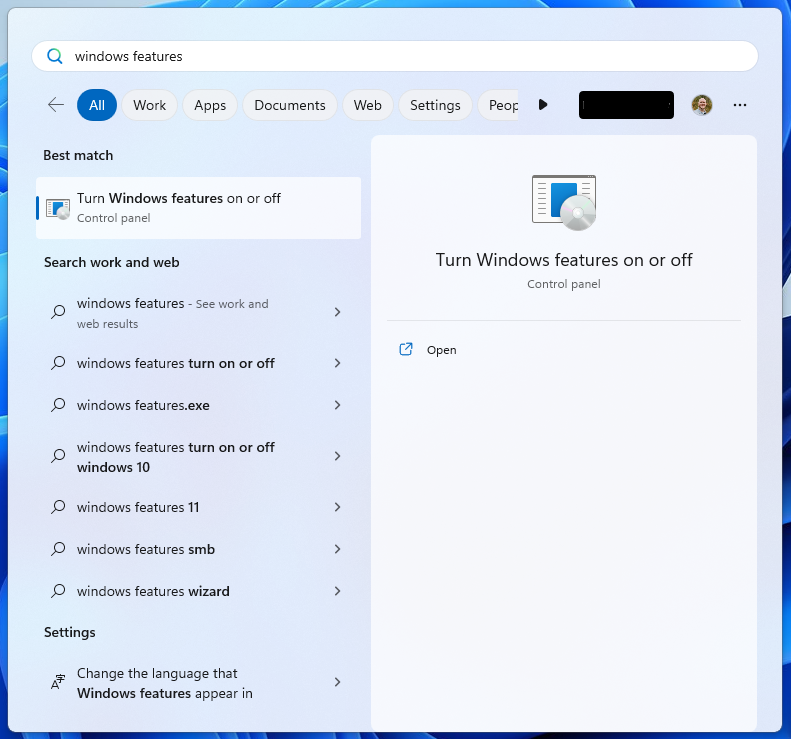
Click on "Turn Windows features on or off" to open the Windows Features dialog.
Scroll down and locate "Windows Sandbox" in the list.
Check the box next to "Windows Sandbox" and click "OK."

Windows will apply the changes and install the necessary components for Windows Sandbox.
Exploring Windows Sandbox Features
Windows Sandbox offers several features that contribute to its effectiveness as a secure testing environment. Let's take a closer look at some of these features:
Isolation: Windows Sandbox operates in an isolated environment, separate from your main operating system. This isolation prevents any potential damage or changes to your system files, registry, or installed applications.
Disposable: Each time you start Windows Sandbox, it creates a clean, fresh instance of the Windows operating system. Any modifications made during a session, such as downloaded files or installed applications, are discarded once you close Windows Sandbox.
Secure Kernel: Windows Sandbox uses a secure, lightweight kernel to provide enhanced security measures. This ensures that any exploits or vulnerabilities within the sandbox environment do not pose a threat to your host system.
Configuring Windows Sandbox
Windows Sandbox offers configuration options that allow you to tailor the sandbox environment according to your needs. By modifying the configuration file, you can customize various aspects of Windows Sandbox. Let's explore some common configurations:
Configured Sandbox: To configure Windows Sandbox, you need to modify the configuration file named "sandbox.wsb." The file is located in the folder: "%UserProfile%\Documents\Windows Sandbox." Open the file using a text editor and make the necessary changes.
Networking: By default, Windows Sandbox uses a virtual network adapter that allows internet access. You can disable the networking feature by setting the "Networking" value to "Disable" in the configuration file.
Shared Folders: You can enable access to specific folders on your host system within Windows Sandbox. Add the following lines to the configuration file, replacing "C:\Path\to\your\folder" with the actual path of the folder you want to share:
xmlCopy code<MappedFolders> <MappedFolder> <HostFolder>C:\Path\to\your\folder</HostFolder> <ReadOnly>false</ReadOnly> </MappedFolder> </MappedFolders>Hardware Acceleration: To enable hardware acceleration within Windows Sandbox, ensure that your host system has virtualization support enabled in the BIOS settings.
Automatic Script Execution: You can set up Windows Sandbox to automatically execute scripts when it starts. For example, you can run a PowerShell script by adding the following lines to the configuration file, replacing "C:\Path\to\your\script.ps1" with the actual path to your script:
xmlCopy code<LogonCommand> <Command>PowerShell.exe -ExecutionPolicy Bypass -File "C:\Path\to\your\script.ps1"</Command> </LogonCommand>This will run the script every time Windows Sandbox starts.
Installing Software at launch in Windows Sandbox: Visual Studio Code
In this example, I wanted to use Visual Studio Code because it is a useful application if we are testing code in our sandbox environment. If you want to have Visual Studio Code or any software for that matter pre-installed in your Windows Sandbox, you can include the installation steps in your script. Here's an example PowerShell script that installs Visual Studio Code:
# Download Visual Studio Code installer
$vsCodeUrl = "https://go.microsoft.com/fwlink/?LinkID=760868"
$vsCodeInstallerPath = "$env:TEMP\vscode_installer.exe"
Invoke-WebRequest -Uri $vsCodeUrl -OutFile $vsCodeInstallerPath
# Install Visual Studio Code
Start-Process -Wait -FilePath $vsCodeInstallerPath -ArgumentList "/silent"
# Remove the installer
Remove-Item -Path $vsCodeInstallerPath
Save this script as a .ps1 file and update the configuration file accordingly. With this configuration, Windows Sandbox will run the script, which will download and install Visual Studio Code during the sandbox startup process.
Quick Recap
Windows Sandbox provides a secure and isolated environment for running untrusted applications and files. By leveraging its features and configurations, you can ensure the safety of your system and protect it from potential threats. Whether you're testing suspicious software or experimenting with code, Windows Sandbox is an invaluable tool that combines convenience with robust security.
By following the steps outlined in this blog post, you can set up, configure, and maximize the potential of Windows Sandbox. Enjoy exploring new software, testing applications, and experimenting with peace of mind, knowing that your system remains safeguarded.
Remember to adjust the configurations and paths in the examples to match your own setup. Stay secure and stay protected.